iOS app to hack and remotely track any WeChat user 
To start the hack, enter the phone number or username of the target WeChat account:
With WeHacker, you can get constant access to the target user's activity data: new messages and calls, time of the last login to the account, movements and much more.
By registering an account through the Dashboard, you automatically accept all the Terms of the User Agreement.
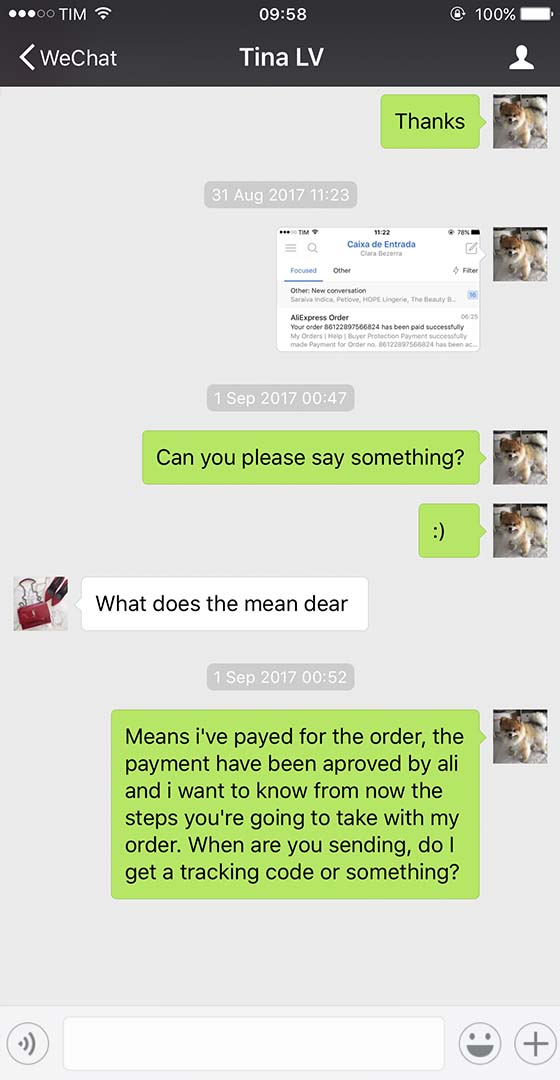
- 20:52 Hello, I was recommended your app🙏
- 20:52 Was told it´s the best way to hack WeChat on the iPhone
-
edited on 20:52
I have a suspicion that
my wife cheats on me - 21:04 Yes, just enter the phone number or username
- 21:04 And launch the session
-





A secure solution for tracking WeChat on iOS
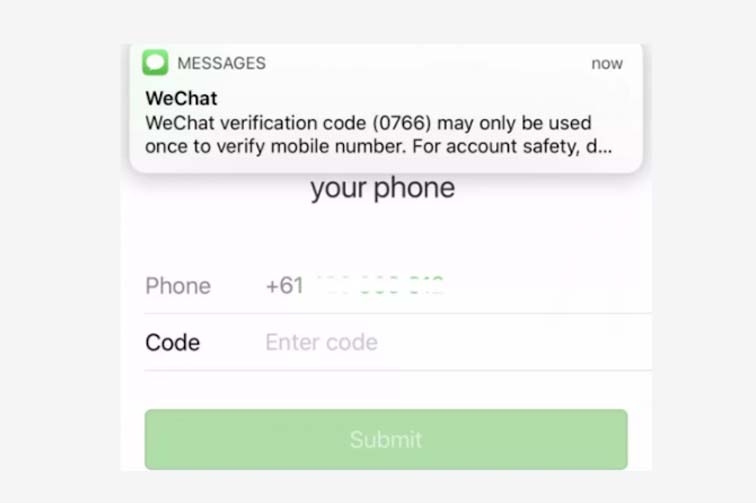
The software gains access to the target account database by intercepting an SMS message with a verification code, which is sent to the linked phone number when access revocery is requested. The code is used to log in to the account, after which all associated data is copied and displayed in WeHacker's Dashboard. This approach allows to protect users from the risk of being detected.
Hacking and controlling someone else's WeChat account on iOS
By launching a hacking and tracking session, WeHacker users gain full control over the specified WeChat account. You can track its entire history, including correspondence, location points, received and sent files. The smart search system uses a module that analyzes correspondence, iCloud data, and optimizes the search for the entered request (keyword).
Wiretapping of incoming and outgoing calls
Audio recordings of calls, information about all personal and group calls, in which the account owner participated, is stored in WeHacker as a table with such possible fields as Call Participants, Call Originator, Time of conversation start, Duration of the conversation. The application notifies users about new calls in the account, and then, in case of an activated wiretap, broadcasts an audio signal to the Dashboard.
Activity tracker and parental control
During the sortware development, we put special emphasis on making it as flexible as possible. We managed to do this, and the flexibility of the software architecture is especially noticeable when setting up and working with the activity tracker: several options are available in the interface to display new activities in the Dashboard; you can create monitoring scenarios in which WeHacker will filter out categories of information that do not interest you.
How does it work?
How to hack WeChat on iPhone without access to iCloud?
WeHacker iOS data tracker has the necessary functionality to track correspondence, location and personal data of the WeChat account without accessing iCloud. You do not need to Jailbreak the device or install any additional software to start tracking. Moreover, by becoming a member of the affiliate program you can hack WeChat on iPhone or iPad for free - all you need to do is to distribute a referral link and then you will receive royalties for each user who buys WeHacker by clicking on it.
Monitoring and controlling activity in WeChat
Tracking account activity and message status
WeHacker activity tracker identifies the time of the last login to the account and the device model from which the login was made. Unlike the WeChat app, the software has the ability to track the status of messages - in the system, messages are displayed with one of three statuses: Sent, Delivered, Read. The same tool also tracks visits to other users' profiles, Moments, added Contacts, and other personal account data.
- 18:33 Hi, I really want to see you ...💋 🔥
- 18:33 Why don't we meet for a coffee? We can figure out a way to spend the evening afterwards.
- My boyfriend went away for a week on a business trip and now I'm completely free💃🏼
- 18:37 Honey, I'll call you as soon as I'm free 😊
Saved documents and media files on iPhone
Access to data stored in the device memory
All important data that you want to access quickly can be added to Favorites. When Synchronization with your device is activated, such chats, files and information will automatically become available offline. iMessages, contacts or iOS locator data are also streamed to Favorites - when new activity related to them is detected, the app will notify you about it in the way you choose (there are 4 types of notifications are available in the system).
Track WeChat circles
Find out who the user is corresponding with
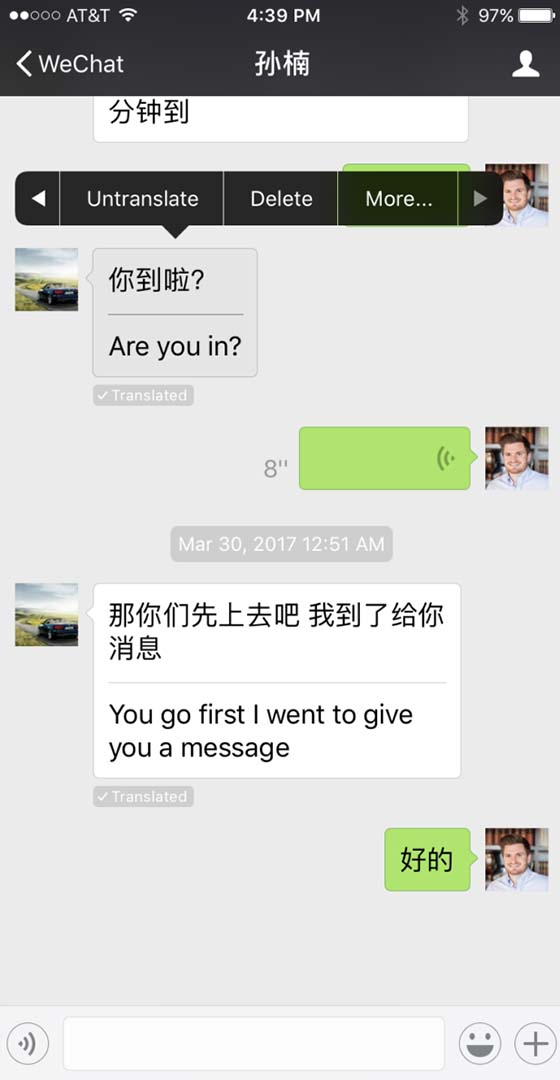
The software analyzes information from the account database and generates statistical summaries from which you can learn who the target user corresponds with most often, whose profiles he visits most often, how much time he spends daily in WeChat, how much money he spends daily (based on WeChat Pay platform data), where he regularly goes in the evening, and more.
Current location
Access to geodata of iPhone, iPad or Mac
The web interface integrates several tools for working with the geodata of devices authorized in a hacked account. The movement tracker displays a person's current location and stores information about places he has visited before. The neural network analyzes the duration of his stay in certain places and determines his home and work addresses, favorite bars, most visited stores, and other types of locations.
How to hack WeChat on iOS
Registration and target designation
The first thing you need to do is enter the phone number that the target account is linked to and wait for confirmation from the software. Then create an account - it is important to provide the correct email address. In addition, remember to allow the web application to access the device's cache, this is important for optimizing its performance.
Selecting a service package and activating the hack
The last step before launching the hack is to pay for the software: several packages are available, varying in the number of active tracking sessions - from one WeHacker account you can simultaneously track up to 5 WeChat-accounts.
Logging in to a WeHacker account
You don't need to download or install anything to log in to the target account and work with the obtained data - all the tools and functions are available in the same browser interface. Immediately after logging in, it is recommended to go to Account Settings and set all the necessary parameters.
Customer Reviews
Read about our customers' experience in the Customer Reviews tab
EVERYTHING IS SUPER! I really didn't expect it to be so easy. I entered the person's number, warmed up, came back, and voila, it really tracked messages, photos, and payments. I'm amazed where the technologies have come to.

That´s an awesome application. I launched the hacking from my phone, then synchronized the app with the phone memory and all the information I need got automatically downloaded so I can use it in transport. I like that the interface is clear and multilingual, it is a big plus.

I needed to read the correspondence of my boyfriend. He is now in China and I suspected that something was wrong there. Through my friends I found out about this program, entered his phone number and paid a standard rate. Well, what can I say, the money I paid was not in vain, my suspicions were justified, the program is good: there are many different opportunities, I think if someone needs it - you can figure out how to use it and keep track of everything that happens in an account.

With WeHacker I set up WeChat tracking for my son, now I know at least a little bit about what he is interested in and doing in life. Plus the app shows me where he is, which makes life better for both of us - I don't worry in the nighttime, and he doesn't get calls from me every half hour.

To be honest, I haven't used WeChat in a thousand years myself and came across WeHacker in a quite tricky way. I urgently needed to find out the password to my sister's laptop, and I was looking for ways to hack the password to one of her accounts, hoping that the password would match. The app worked like a charm, about half an hour after signing up I was able to trace the authorization data, which luckily matched the laptop as well.

Who would have thought that WeChat could be hacked so easily! Just half an hour of time, a very reasonably priced payment and voila, I'm already reading the person's correspondence live. I have been using it for over a week now, so far everything is going good. Cool and very innovative))
Frequently Asked Questions
Answers to questions that can appear while using the software:
- Is it possible to use a device geolocation tracker to track a lost iPhone or iPad via WeChat?
- WeHacker is the optimal solution for WeChat account geodata tracking. All data about the location of the lost device will be displayed on web maps in real time with a maximum accuracy of 3 square meters.
- Does the app allow access to the data of authorized devices?
- The software keeps track of all the device data to which it has access: iCloud passwords, iMessages conversations, photos and videos from the device's Gallery, and a collection of geotags. Access, in turn, is determined by whether the WeChat app has permission to view the files.
- How likely is it that the iOS security system identifies tracker activity as suspicious activity?
- The app does almost no interaction with the device's security system, since all interaction with its tools is provided through the browser. From the browser security point of view, WeHacker is a secure web application, and data tracking is not identified as suspicious activity.
- Does the software have any system requirements regarding the version of the iOS operating system?
- The OS version is not crucial for the stable functioning of the application. However, for an optimal experience with the software, we recommend using the most up-to-date version of the operating system.
- Do you need to give the app access to any of the files or functions on the device?
- WeHacker does not require access to the iPhone or iPad Locator or device memory (permission is required to Synchronize data between the iOS device and the account database). The program will work steadily without these permissions.
We automatically convert payments that are accepted in other currencies.